Autonomous
Uncontainable
Sovereignty over the sky
Introducing
Surge C-UAS
weaponised drones are making airspace unpredictable
Borders, infrastructure, and critical operations now face a new layer of vulnerability, the low-altitude battlefield.

built from the ground up
No outsourcing. No vendor lock-in. From circuit boards to AI algorithms, we control the entire stack.
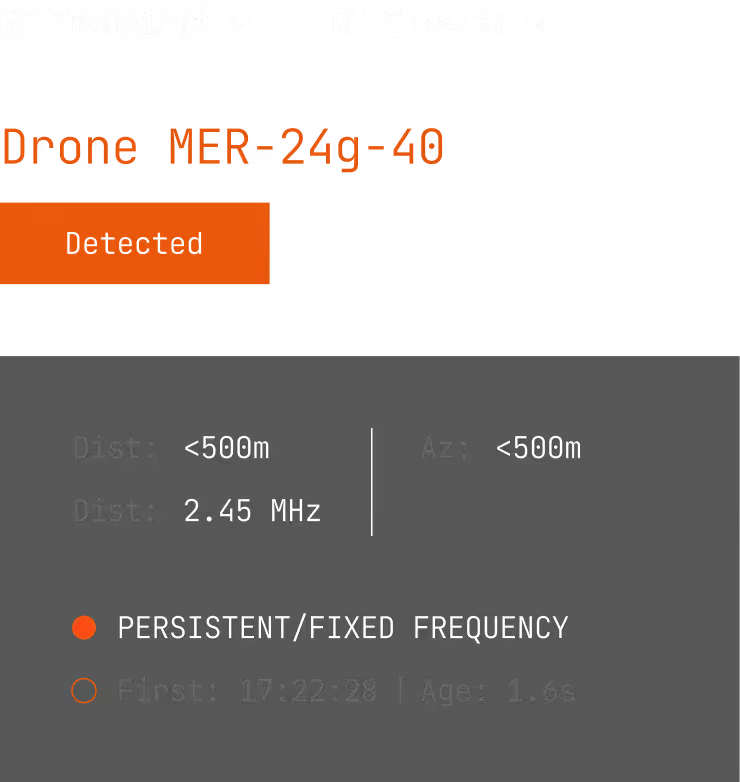
Threat detected. Signature verified. Response deployed. In Seconds.
Simultaneous multi-threat detection. 24/7.
Precision jamming. Single frequency, specific band, or full spectrum.
All-weather operational. -30°C to +50°C. 95% humidity.
One system. Any terrain. Mission-ready.
Swap modules in the field. Antennas, power units, upgrades. Mission-specific configuration.
Operational in under 60 seconds. Unpack and deploy.
Comprehensive mission suite. Electronic countermeasures. Direction finding. Geolocation.
One unit sees. All units know. Network responds.
Distributed coordination. Multiple units work as one. Optimised coverage across terrain.
Shared intelligence. Threat data, geolocation, RF signatures. Instant network-wide awareness.
Configurable alerts. Operators see priority threats only. No noise.
Self-learning architecture. Regular updates. Always ahead of the threat.
Detailed intelligible system logs. Full visibility into every decision. coordination.
Deploy anywhere. Cloud, on-premises, or edge. Performance scales.
Complete threat intelligence. New threats, RF signatures, communication patterns. Learns continuously.


